 A malicious Python package disguised as a legitimate Telegram development tool has been identified as a backdoor capable of granting attackers remote control over compromised systems, raising fresh concerns about supply chain vulnerabilities in open-source ecosystems.
A malicious Python package disguised as a legitimate Telegram development tool has been identified as a backdoor capable of granting attackers remote control over compromised systems, raising fresh concerns about supply chain vulnerabilities in open-source ecosystems.Security researchers have uncovered that the package, named “pyronut”, was uploaded to the Python Package Index while posing as an alternative to Pyrogram, a widely used framework for building Telegram bots and userbots. Pyrogram is a trusted MTProto API client relied upon by developers to automate messaging, manage accounts, and build services on Telegram’s infrastructure.
Analysis shows that pyronut embeds hidden functionality enabling remote code execution on infected machines. Once installed, the malicious code establishes a covert channel that allows attackers to execute commands not only within the Telegram session but also on the host system itself. This effectively turns compromised environments into remotely controlled endpoints.
The attack exploits a familiar tactic in the software supply chain: typosquatting and imitation. By mimicking the naming convention and purpose of a legitimate package, pyronut increases the likelihood that developers may inadvertently install it, particularly when searching for alternatives or enhancements to existing tools. The risk is amplified in fast-moving development environments where dependencies are frequently added without deep scrutiny.
Researchers indicate that the malicious package hooks into Telegram bot logic, allowing attackers to intercept messages, manipulate bot behaviour, and potentially exfiltrate sensitive data. Because Telegram bots often handle credentials, API tokens, or user interactions, the compromise can extend beyond a single system to broader networks or services connected to the bot.
Technical assessments reveal that the payload activates upon installation, embedding itself within the runtime environment. It communicates with attacker-controlled infrastructure, enabling command execution and persistence. This level of access means that attackers can deploy additional malware, harvest system data, or pivot laterally within a network.
The emergence of pyronut highlights a growing trend in targeting developer ecosystems rather than end users directly. Open-source repositories such as PyPI, npm, and others have become critical infrastructure for modern software development, but their openness also creates opportunities for abuse. Malicious actors increasingly exploit trust in widely used libraries to distribute harmful code at scale.
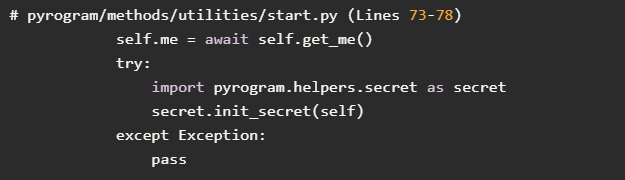
Cybersecurity analysts note that such campaigns are difficult to detect at first glance because the malicious components are often obfuscated or hidden within otherwise functional code. In the case of pyronut, the package appeared to provide legitimate Telegram functionality while quietly embedding its backdoor mechanism.
Industry experts warn that the impact of these attacks extends beyond individual developers. Organisations deploying applications built on compromised dependencies may unknowingly expose production systems, customer data, and internal infrastructure to external control. This raises questions about dependency management practices and the need for stricter verification processes.
Efforts to mitigate these risks have intensified across the software industry. Package repositories have introduced automated scanning tools and stricter publishing policies, while security firms continue to monitor for suspicious uploads. However, the volume of new packages and updates makes comprehensive oversight challenging.
Developers are being urged to adopt defensive measures, including verifying package authenticity, reviewing source code where possible, and relying on well-established libraries with active maintenance communities. The use of dependency scanning tools and software bill of materials frameworks is also gaining traction as a way to track and audit components within applications.
The pyronut incident also underscores the importance of runtime monitoring. Even when malicious code slips through initial checks, behaviour-based detection systems can identify unusual activity such as unexpected outbound connections or unauthorised command execution.
Telegram’s popularity as a platform for automation and communication has made it an attractive target for threat actors. Bots are widely used in sectors ranging from customer service to financial trading and community management, often operating with elevated permissions. A compromised bot can therefore act as both an entry point and a propagation vector.
Security researchers emphasise that vigilance is required at every stage of the development lifecycle. From dependency selection to deployment and monitoring, each step presents potential exposure points that attackers can exploit.
Topics
Technology
