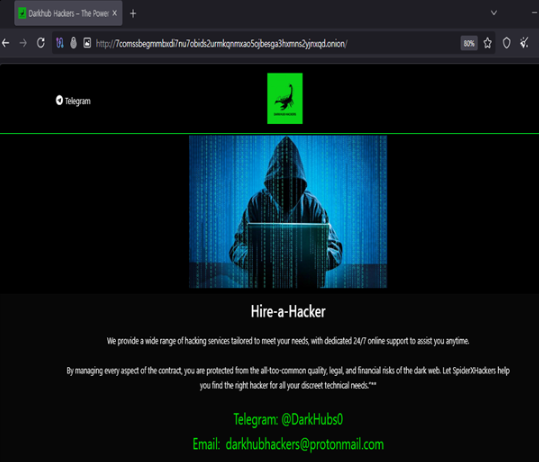
 Darkhub, a newly identified dark web portal, is promoting hacking-for-hire services that claim to offer account takeovers, surveillance, cryptocurrency fraud support and financial manipulation, underscoring the growing professionalisation of illicit cybercrime markets.
Darkhub, a newly identified dark web portal, is promoting hacking-for-hire services that claim to offer account takeovers, surveillance, cryptocurrency fraud support and financial manipulation, underscoring the growing professionalisation of illicit cybercrime markets.The platform, reachable through the Tor network, presents itself as a structured marketplace for offensive digital services aimed at individuals and organisations. Its listings include access to email accounts, Instagram, Telegram and WhatsApp profiles, mobile monitoring, communication interception, location tracking, cryptocurrency schemes and services framed as fund recovery.
Security analysts examining the portal have noted that the platform uses a polished interface and service-style categories to project credibility. Yet several of its offerings carry signs commonly associated with advance-fee fraud, where buyers are persuaded to make upfront payments for services that may never be delivered. The inclusion of “credit score manipulation” and “fund recovery” claims is especially notable because similar pitches are often used to target people who have already lost money in online scams.
Darkhub’s emergence illustrates a broader shift in cybercrime, where underground actors increasingly package illegal capabilities in the language of mainstream digital services. Instead of requiring technical expertise, buyers are offered menus, categories and apparently fixed services, lowering the barrier for disgruntled insiders, fraudsters, stalkers and financially motivated criminals.
The platform claims to provide compromise services for social media and messaging accounts, a category that remains one of the most visible segments of the hacking-for-hire economy. Such attacks often rely on phishing, leaked credentials, social engineering or malware rather than elite technical intrusion. Account takeover can expose private messages, reset linked services, enable impersonation and create reputational damage for victims.
Surveillance-related listings raise additional risks. Darkhub advertises mobile device monitoring, message interception and tracking of communications, pointing to an overlap between cybercrime, stalking, coercive control and corporate espionage. Even when such portals exaggerate their abilities, the demand they cultivate can fuel real-world harm by encouraging buyers to seek unauthorised access to personal devices and private data.
The financial-fraud component is equally significant. Cryptocurrency-related services, unauthorised account access and fund-recovery claims reflect the way cybercrime markets have adapted to the expansion of digital assets. Fraudulent recovery schemes often promise to retrieve stolen crypto or reverse losses, only to demand fresh payments from victims. These operations can extend the damage from an initial scam by extracting more money, personal documents and wallet information.
Infrastructure clues add another layer to the case. Analysis of Darkhub has identified signs that its back-end systems may not be fully isolated inside anonymised networks. A publicly routable IP address linked to supporting infrastructure suggests possible exposure beyond Tor, creating both operational risk for the actors behind the platform and investigative opportunities for defenders and law enforcement. Hosting choices associated with permissive or lightly enforced environments are frequently attractive to threat actors seeking resilience against takedowns.
Darkhub also fits a long-running pattern in which many hacking-for-hire portals are themselves scams. Past academic and industry research into such markets found that only a minority of tested services actually attempted account compromise, while many operators simply collected money, stalled customers or disappeared. That does not make the ecosystem harmless. Buyers may still disclose target details, pay criminals, encourage attacks and become vulnerable to blackmail by the same operators they approach.
Cybercrime-as-a-service has matured around stolen credentials, phishing kits, infostealer logs, carding shops, ransomware access brokers and crypto-laundering services. Marketplaces trading stolen browser passwords, session tokens and identity packs have made account takeover easier for low-skill actors. Darkhub appears to sit within this ecosystem by bundling several illicit promises into one portal rather than specialising in a single category.
For organisations, the case reinforces the need to treat personal account security, executive protection and credential exposure as part of enterprise risk management. Multi-factor authentication resistant to phishing, rapid password resets after breaches, dark web monitoring, employee awareness, device security and clear procedures for reporting suspected compromise remain central defences. For individuals, unsolicited recovery offers, claims of guaranteed hacking services and demands for cryptocurrency payments should be treated as warning signs.
Law-enforcement agencies face persistent challenges in tracking actors who use Tor, cryptocurrency payments, offshore hosting, disposable identities and layered infrastructure. Yet such platforms often make mistakes, including exposed servers, reused aliases, poor operational security and links to known hosting providers. Those mistakes can become important investigative leads.
Topics
Technology
